Setting Up authentication for OpenID Connect with Microsoft Azure
Adding a Microsoft Azure Application
1.Log into https://portal.azure.com.
2.Create a new Active Directory or use an existing Active Directory.
3.From App Registration, create a new Application Registration and provide the following information:
•Name: A contextual name for the application, such as ISM Prod.
•Redirect URI: Select the option Web and enter the ISM tenant URL in the format - https://{tenant_url}/handlers/sso/OIDC/AuthResultHandler.ashx.
Configuring a Microsoft Azure Application
1.Open the Microsoft Azure application you just created in the previous section and provide the following information:
Once the above configuration is done, go to Overview > Endpoints, you need to refer to these endpoints while configuring OpenID Connect in ISM.
For more information on Microsoft Azure setup, refer to Microsoft help documents.
Creating a Service Manager Authentication Provider
1.From the Configuration, click Configure > Security Controls > Authentication Providers to open the Authentication Providers workspace.
2.From the New Record Menu drop-down list, select New OpenID Connect.
3.Enter data into the fields:
| Field | Description |
|---|---|
| Default |
Specifies if this authentication provider is called. Automatically set by the application. You change this in the list. To make this authentication provider as the default value, you must first change the default setting for all other authentication providers to false and then change the default setting for this authentication provider to true. |
| Disabled | Specifies if this authentication provider is disabled. |
|
Name |
The name of the OpenID Connect provider. This can be any value you want and will get displayed to the end users on the login page. |
|
Authentication URL |
Enter the value from the OAUTH 2.0 Authorization Endpoint from the Microsoft Azure application created in the above section. Service Manager must be able to initiate an outbound HTTPS (port 443) connection to this URL. |
| Token Verification URL |
Enter the value from the OAUTH 2.0 Token Endpoint from the Microsoft Azure application created in the above section. Note: Service Manager must be able to initiate an outbound HTTPS (port 443) connection to this URL. |
|
Logout URL |
Enter: https://login.microsoftonline.com/{Active-Directory-ID}/oauth2/logout. {Active-Directory-ID} - get this input from the Azure Active Directory properties created in Adding a Microsoft Azure Application section. |
| Session Renewal URL |
The URL to request to renew the session. If this field is empty, the application uses the value of the Authentication URL field. For Azure AD, this can normally be left blank. Note: Service Manager must be able to initiate an outbound HTTPS (port 443) connection to this URL. |
| Client ID | Enter the Microsoft Azure client ID. Get this information from the Application ID field of the Microsoft Azure application created in the above . |
| Client Secret | Enter the secret key that you copied and saved while configuring certificates and Secrets for the Microsoft Azure application created in the above section. |
| OIDC Hosted Domain | Not applicable. |
| OIDC Realm | Not Applicable. |
| Certificate URL |
The URL of the certificate used to verify the signature of the authentication response. Currently, Azure uses this URL: https://login.microsoftonline.com/common/discovery/keys Note: Service Manager must be able to initiate an outbound HTTPS (port 443) connection to this URL. |
| Certificate Issuer |
The name of the certificate authority who issued the certificate. Enter this hyperlink: https://sts.windows.net/{Active Directory ID}/. {Active-Directory-ID} - get this input from the Azure Active Directory properties created in Adding a Microsoft Azure Application section. |
| Expiration Date |
The expiration date of the certificate. Not used in this release of Service Manager. |
| Auto Provisioning | Check to enable. |
| Profile Information URL |
Not used for Microsoft Azure. |
| Auto Provision Role |
Role associated with the new user. |
| Auto Provision Status |
Status of the new user. |
| Auto Provision Team |
Team associated with the new user. |
| Auto Provision User Business Object |
Type of user record to create. Can be either employee or external contact. |
4.Optional. To be redirected to an application URL after successful logout, append ?post_logout_redirect_uri={Redirect URI} to the logout URL. For example, enter https://login.microsoftonline.com/{Active-Directory-ID}/oauth2/logout?post_logout_redirect_uri=https://my_tenant1.saasitdev.com/handlers/sso/OIDC/AuthResultHandler.ashx.
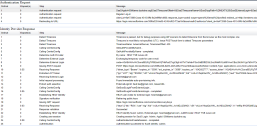
5.Click Save. Your ISM auth provider page should look similar to the image below:
6.To verify the authentication, click Test Authentication. (note you must have an Employee record with an appropriate External Auth linking it to this provider before the test will be fully successful).
•If a line appears stating "Receiving External Login", use Sub as external login as e-mail is not available at this step."
•You may also be prompted to consent to the needed access and will need to log in as an Azure AD admin to accept on behalf of your organization.
•A successful test will look similar to the following screenshot:
Security Considerations When Using Microsoft Azure
Service Manager application servers must be able to initiate outbound connections to the following endpoints:
•Token verification URL
•Certificate URL
All URLs have the following URL pattern: https://login.microsoftonline.com/*.